Question
Who among the following sits at one of the extreme
ends? Study the following information carefully and answer the questions given below: Seven persons A, B, C, D, E, F and G are sitting in a row facing towards the north but not necessarily in the same order. Each one of them likes different shoes i.e., Reebok, Nike, puma, Levis, adidas, woodland and Bata but not necessarily in the same order. The one who sits immediate right of D likes Bata. D sits 2nd from one of the extreme ends. Only one person sits between D and C. A sits 4th to the left of G, who sits adjacent to C. Only one person sits between F and G, who likes puma. More than three persons sit between A and F. More than two persons sit between the one who likes puma and the one who likes Levis. B sits to the left of E. B is not an immediate neighbor of A. Neither D nor C likes woodland. The one who likes Reebok sits 3rd to the left of the one who likes woodland. E does not like Nike.Solution
As per the given information, the one who sits immediate right of D likes Bata. D sits 2ndfrom one of the extreme ends. Only one person sits between D and C. Here we have two possible cases i.e. 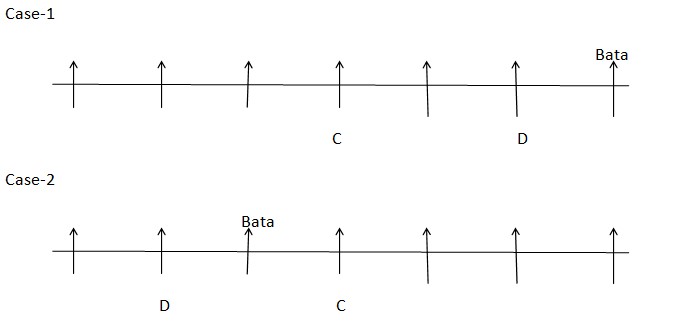 A sits 4th to the left of G, who sits adjacent to C. Only one person sits between F and G, who likes puma.
A sits 4th to the left of G, who sits adjacent to C. Only one person sits between F and G, who likes puma. 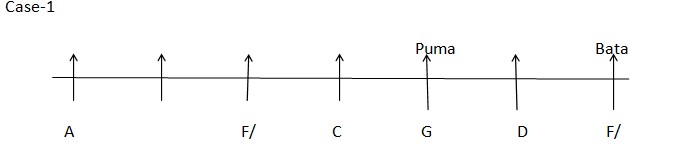 Case-2
Case-2 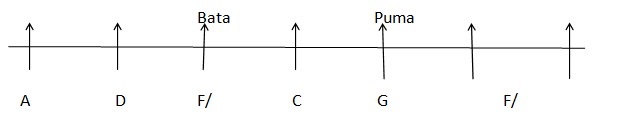 More than three persons sit between A and F. B sits to the left of E. More than two persons sit between the one who likes puma and the one who likes Levis.
More than three persons sit between A and F. B sits to the left of E. More than two persons sit between the one who likes puma and the one who likes Levis. 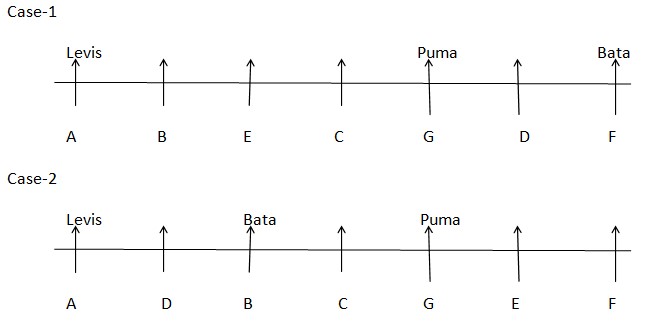 B is not an immediate neighbor of A. Here Case 1 gets eliminated. Neither D nor C likes woodland. The one who likes Reebok sits 3rd to the left of the one who likes woodland. E does not like Nike. So the final arrangement will be,
B is not an immediate neighbor of A. Here Case 1 gets eliminated. Neither D nor C likes woodland. The one who likes Reebok sits 3rd to the left of the one who likes woodland. E does not like Nike. So the final arrangement will be, 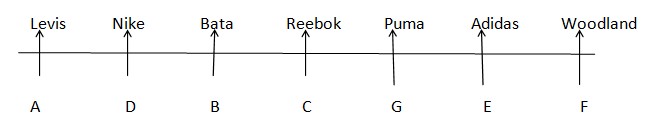
Consider a system with 4 CPU cores. If there are 8 user-level threads in a single process, what is the maximum number of these threads that can execute ...
Which type of polymorphism in Java is achieved through method overloading?
Which of these is a key characteristic of SaaS (Software as a Service)?
In public-private key encryption , which of the following is true regarding the private key ?
Which I/O scheduling algorithm is designed to reduce the average response time for disk operations by prioritizing requests based on proximity to the cu...
Which statement is FALSE regarding DRAM memory?
Which of the following is a property of an admissible heuristic in A* search?
Fill in the correct option for 28 blank space.
In a backtracking algorithm, what happens when a partial solution is found to violate a constraint?
The Naive Pattern Searching algorithm has a worst-case time complexity of O(MN), where 'M' is the length of the pattern and 'N' is the length of the tex...
Relevant for Exams:



